Fraud is a threat in every geography and every industry. The victims are individuals, families, government institutions, private businesses, non-profit organizations.
Fraud is also a growing problem. Europol considers fraud schemes to be among the fastest growing criminal threats in Europe. And in PWC’s 2020 global survey on fraud and financial crime, the number of respondents who had recently experienced fraud was the second highest in 20 years. Reports also indicate that the amounts lost to fraud scams are increasing overall.
Understanding a problem is the first step to understanding it. This article takes a deep dive into fraud: defining what it is, understanding its cost, and examining the profile of a fraudster. We’ll also explore how to effectively detect fraud and how to carry out a fraud investigation with next generation fraud analytics.
Fraud is the intentional use of deception to obtain an unlawful or unfair advantage. The intentionality is important here: this is what differentiates fraud from error. We consider actions fraudulent when someone conceals assets or commits an act of deception for financial gain.
Fraud falls under the umbrella of financial crime, and it’s a very broad criminal category. There are almost countless ways that criminals can and do commit fraud. Fraud can include anything from insurance fraud to credit card fraud to identity fraud—and the list goes on.
There are three principal categories of fraud.
- First-party fraud is basically impersonation, when a person signs up for an account with information that is entirely or partially fictitious or stolen.
- Second-party fraud is when someone commits fraud using someone else's credentials, with that person's knowledge.
- Third-party fraud happens when an organization’s customers are the victims, through stolen or hacked account information or card credentials, for example.
The ways criminals defraud their victims are ever changing. New patterns and techniques emerge all the time, making it a challenging category of crime to combat.
Fraud is expensive. While the covert nature of the crime means no one knows precisely how much it costs, studies show an average organization can expect to lose 3% to 6% of their profits to fraud, but that can rise to 10% for some businesses. Global losses equate to over 6% of the GDP.
Fraud costs businesses as both direct and indirect losses, and in the form of anti-fraud expenses.

Too many fraudsters fly under the radar, and the assets they steal go undetected, for us to know how much these crimes really cost.
According to reliable estimates, though, the amounts lost to fraud are huge.
According to the ACFE, 21% of cases caused the victimized business to lose at least $1 million. And global losses are increasing: since 2009, losses due to fraud have risen by 56.5%.
The financial cost of fraud can go far beyond what is stolen. Businesses can lose their reputation and their customers along with it. Fraud can also result in loss of market position, loss of future opportunities, low employee morale, lawsuits, and more.
Prevention, detection, and investigation are also costly. For online fraud alone, it is expected that these costs will reach $9.3 billion by 2022. Within financial institutions, these costs have been steadily increasing. In 2020, the average bank spent $3.78 for every dollar lost to fraud.
All these numbers sound alarming—and they are. But fraud costs are in part preventable. The huge amounts of lost resources and money spent on prevention also represent an opportunity. With the right tools and procedures, fraud is a cost that can be managed like other business costs. And effectively managing fraud and the cost of prevention can mean a more successful, more profitable business.
Even if the variety of schemes and scams makes fraud difficult to pin down, there are common threads and patterns that can make it easier for organizations to spot and prevent fraud, or prevent problems from getting worse.
The fraud triangle helps understand who might commit fraud. There are three common elements to many of these crimes: pressure, opportunity, and rationalization. All three of these elements must come together at the same time for fraud to occur. Sometimes a fourth element is included: capability.
Pressure refers to the elements that might incite a person to commit fraud. This might be pressure from within an organization: pressure to deliver certain results or bonuses tied to performance. Pressure may also come from a fraudster’s personal life: personal debt, a gambling problem, etc.
Opportunity is the circumstances within an organization that allow fraud to occur. This may include a lack of internal controls, poor approval processes that leave open opportunities to commit fraud, poor accounting policies, etc.
Rationalization is the means by which a fraudster justifies an act of fraud to herself or himself. They might rationalize by saying that they have no choice given the circumstances, that other people in their organization are doing the same thing, or that their behavior will simply go unnoticed.
Capability refers to the idea that a person must have both the character traits and the knowledge of processes and controls to commit fraud.
Like any other type of crime, fraudsters are not limited to one type of person. If that were the case, fighting fraud would be much easier.
There are certain traits that connect many fraudsters, however. Understanding these traits can help an organization understand who might be more likely to commit fraud and manage risk accordingly.
Commonly, fraudsters are male, have a university degree, and are between the ages of 31 and 45. They have exhibited no prior warnings. And they have been with their company for five or more years.
While these traits can be helpful guidelines, it’s essential to keep in mind that there are a wide variety of fraudsters, and they do not all fit this profile.
One of the most basic methods for preventing and detecting fraud is understanding what constitutes a red flag.
A situation that seems too good to be true, that promises very high returns, that demands upfront payments, or that creates a sense of urgency may be a red flag. So is a gut feeling that something isn’t right.
Employee behavior red flags include living beyond his or her means, financial difficulties, taking work home, and spending time in the office alone outside of work hours.
Red flags are warning signs, but they are not proof of guilt.
It would be impossible to name all the possible fraud schemes. One of the major challenges for fraud leaders is the agility and creativity of fraudsters. It can seem like once you get a handle on one type of fraud, another threat pops up. Fraudsters are experts at exploiting any and all new opportunities.
Still, there are many known and relatively common fraud schemes. Just about any of these common fraud schemes can be internal, external, or collusion, where an insider works with external collaboration.
Common fraud schemes include, but are not limited to: procurement or contract fraud, corporate asset misappropriation, financial statement fraud, ponzi schemes, bank fraud, securities fraud, cyber fraud, and social engineering.
Despite ramped up efforts, fraud leaders are struggling to manage risks and losses. Why is that, and why are organizations experiencing more and more fraud?
Fraudsters are better and better organized, operating within complex networks. Many criminal organizations also work internationally. Europol found in a recent report that 7 out of 10 criminal groups are active in more than three countries.
What does that look like in the real world? A Romanian fraud network based in Mexico could use Russian technological expertise to defraud victims, use money mules in many countries to transport the illicit proceeds, which are then laundered through real estate in the US and Brazil.
Detecting such sophisticated scams is very challenging.
Fraudsters also adapt their tactics to evade simple rules. Fraud incidents are increasing overall, and organizations are seeing evolving and more complex schemes emerging as criminals take advantage of new opportunities. Synthetic identity fraud is one example of a typology that is especially difficult to detect; synthetic identities mix elements of real identities with false or stolen elements, giving them the appearance of legitimacy when a fraudster tries to open a bank account, for example. Fraudsters also use collusion with insiders and networks of many accomplices to scale the exploitation of any weaknesses.
A fraud risk assessment enables you to identify where fraud might occur and who might be a likely fraudster. Assessing fraud risks is an essential step in managing fraud, since it allows you to identify gaps and weak points in your defenses. Formal risk assessment is required by some compliance regulations. It is also considered a best practice within many industries.
Each fraud risk assessment will differ based on the nature of your organization, geography, and plenty of contextual elements. A risk assessment must therefore be customized.
The basic formula for risk assessment is: inherent risk - control effectiveness = residual risk.
To do an effective assessment, you must identify all potential risks. To do so, you have to think like a fraudster to identify any and all opportunities for criminal activity. Your risk assessment should also evolve over time, since fraud risks can change quickly and dramatically.
Risk assessment is an opportunity to proactively identify threats before a crime occurs. Doing this exercise shines a light on vulnerabilities. It can also help break down silos within your organization, since it requires reaching out to other functions to gain a full understanding of risk.
Even if it’s impossible to eliminate all fraud risk, organizations can mitigate that risk. Fraud is a vast and often complex type of crime, so managing fraud risk requires a multi-level, multi-step approach.
Establishing multiple lines of defense gives your organization better chances of catching fraudsters.
People are one face of the coin. Having a combination of management, risk managers, and external auditors as part of your anti-fraud model means more eyes on the lookout for fraud risks, and creates the possibility of cross-checks. For these lines of defense to be effective, the people and teams involved in combating fraud must communicate to make sure they are not working in silos.
The other face of the coin is technology. Multiple tools are needed to cover vulnerabilities in the face of clever criminals. Simple rules-based alert systems are great at quickly flagging suspicious activity, but they aren’t effective at detecting new threats. An investigation platform like Linkurious Enterprise can look at the broader context around people and transactions to identify suspicious connections and uncover smart criminals.
Fraud leaders are constantly looking for ways to beat new criminal techniques. The criminals then often find ways around those new defenses, and so on.
It’s a bit like a defense in depth military strategy. Instead of having all defenses on the front line for an enemy attack, defenses are spread out. As the enemy advances, they meet resistance after resistance, causing them to lose momentum and strength. Similarly, deploying multiple lines of defenses against fraud increases the chances of preventing or detecting an attack and helps mitigate damages.
A best practice for managing fraud risk is understanding who you are doing business with, be it your customers or the vendors you’re working with.
In some industries, like banking, having Know Your Customer (KYC) policies in place may be required for compliance reasons. Even when it’s not the case, KYC - also called customer due diligence, or CDD - is a best practice to help prevent fraud.
KYC is a set of activities done during onboarding that help ensure an organization knows who their customers are and the potential fraud risk they may pose. This also helps determine what normal behavior looks like for a new customer. Having a baseline of normalcy helps flag anomalies down the road.
Similarly, it’s important for organizations to vet their vendors. Not only can vendors defraud an organization, but businesses can be held liable for vendor misconduct. Before doing business with an outside provider, you should screen for adverse media, politically exposed persons (PEPs), look into ownership structure, and be on the lookout for operations in high-risk industries or geographies.
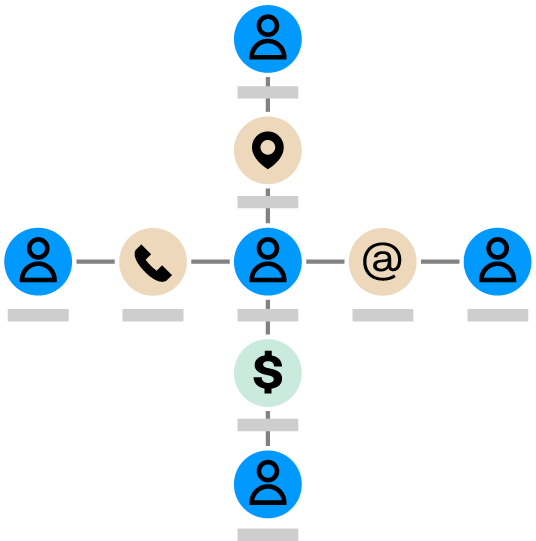
Organizations often consider transactions, behaviors, businesses, and individuals in isolation for fraud detection. They may look at the number of transactions an individual or business has conducted within a given timeframe, for example, and consider anything over a certain limit a potential fraud red flag.
But considering information in isolation isn’t enough. Without a holistic view of wider networks and relationships, it’s difficult to detect and stop sophisticated fraud tactics that are designed to evade simple rules.
Say someone requests a loan from your bank, and she seems normal, passing all the standard checks. You grant her the loan. What you couldn’t see was that her address, phone number, and IP address are all indirectly connected to a known fraudster. She turns out to be an accomplice working in the same fraud network as him.
When you discover suspicious activity within your organization - be it through your fraud monitoring system, a whistleblower, or some other means - the next step is to investigate to understand if an act of fraud has occurred or not.
Fraud monitoring systems tend to generate high numbers of false positives, so it’s important to allocate investigative resources to alerts that seem legitimate or higher risk. An investigation platform like Linkurious Enterprise can speed up both case triage and investigations by showing you the full context around each suspicious activity alert.
When investigating fraud, all steps in the investigation need to be documented. Documenting fraud investigations is essential for building a case should law enforcement need to investigate further.
In case the fraud is confirmed, you’ll also need to investigate how the fraud occurred. What controls were in place, and how were they bypassed? Gaining a full understanding of all fraud incidents is an opportunity to improve controls and defenses going forward.
Fraud leaders often experience limitations with traditional detection and investigation systems, which fail to analyze deeper connections within data. The result is fraud cases that slip through the cracks.
Graph analytics is an approach in which data is structured as a network. Information is stored as nodes, which are connected to each other by edges that represent the relationships between them. Graph analytics thrive on high levels of complexity and use advanced algorithms to connect the dots between multiple data points and sources to find suspicious connections.
Anti-fraud applications generally connect simple data points to detect and flag suspicious behavior. This might be connecting an IP address to a user, withdrawal activities to a place of residence, or a loan request history to a client.
These systems fall short on complex analysis involving several layers of relationships or multiple data types. The relational databases that emerged in the 80s aren’t built for this type of analysis. They are efficient at storing and analyzing tabular data, but their underlying model makes it difficult to connect data scattered across multiple tables and analyze that data as a network.
Graph technology, on the other hand, is built for this purpose. This data model is particularly well suited to organize and analyze data where connections are as important as individual data points.
A graph structures data as nodes and relationships, also called edges. Each node represents a single data point like a person or an address. Each edge represents how two nodes are connected, like a person living at an address.
Using graph algorithms, you can quickly answer many of the questions relevant to fraud investigations. Is one of your clients indirectly connected to a politically exposed person? A pathfinding algorithm will reveal if they are. Who is the leader of a group of fraudsters? A centrality algorithm will show you who is most likely to be the ringleader. Is a given fraudster actually part of a bigger network? A community detection algorithm can help you understand if they are.
Graph data is also easy to explore, since a graph visualization provides a complete overview of different entities and all the connections between them in a single view.
Graph technology enables analysts and investigators to detect complex fraud patterns that might otherwise go unnoticed. It also speeds up investigations by eliminating the need to manually seek out information from different sources.