Consumer payment habits have shifted fast over the past few years, and few financial products reflect that shift more clearly than buy now, pay later (BNPL). Platforms like Klarna, Affirm, Zip, Flex, and Afterpay have built enormous user bases by offering a simpler alternative to credit cards, letting customers spread the cost of purchases across installments without interest.
BNPL transaction values reached $334 billion in 2024 and are projected to more than double to $687 billion by 2028, according to Juniper Research. But rapid adoption comes with risk. The same features that make BNPL attractive to consumers, like speed, simplicity, and minimal friction at checkout, also create openings that fraudsters are quick to exploit.
This article explores what exactly makes short term lenders vulnerable to fraud, as well as the types of buy now, pay later fraud providers typically face. We’ll also look at how network analytics are a key piece of the puzzle for more efficient fraud detection and investigation.
Buy now, pay later, or BNPL, lets customers pay for goods in increments. Instead of paying for a purchase in full upfront, payment is broken down into smaller installments, typically without interest. The BNPL provider pays the merchant in full upfront and then collects those installments from the customer over time.
The appeal is clear: for consumers, it offers a flexible alternative to credit cards. For merchants, offering BNPL at checkout increases conversion and average order value. That combination has driven adoption across retail, electronics, travel, and even groceries.
The same features that define the BNPL user experience create structural vulnerabilities that bad actors are quick to find and exploit.
Several features of BNPL make it more exposed to certain fraud types than traditional payment methods.
First, credit decisions are made in real time using internal algorithms that work on available customer information. This speedy approval is a must for BNPL platforms to deliver the easy user experience customers expect. But this also makes it easier for bad actors to slip through the cracks.
Second, the installment structure also creates more attack surface than a single transaction. While a standard e-commerce payment happens once, a BNPL transaction may unfold across four, eight, or ten separate payments, each of which represents a potential point of exposure.
Finally, buy now, pay later platforms conduct few formal credit checks. Banks and traditional creditors typically run in-depth checks on customers before granting them credit. BNPL providers instead rely on algorithms and scoring engines to perform credit checks. If the algorithms aren’t perfectly tuned to the tactics fraudsters are using, it can open the door to increased fraud risk.
Buy now, pay later has proven to be especially vulnerable to certain types of fraud: synthetic identity fraud, account takeover fraud, and new account fraud. Beyond these external attacks, providers also face risks from within their own customer base, in the form of first party fraud and friendly fraud. While none of these fraud schemes were invented for BNPL, the nature of this payment model makes it particularly exposed to all of them.
A synthetic identity combines real and fabricated personal information, such as a real address paired with a fake name, into a profile that doesn't correspond to any single real person.
Fraudsters use these identities when purchasing goods with BNPL to pass platform checks, receive goods immediately, and then disappear with no intention of repaying. Because the identity doesn't belong to a real individual, tracking the perpetrator down is extremely difficult. In the first half of 2024 alone, synthetic identity fraud surged by 26%, according to ACI Worldwide.
Account takeover fraud, or ATO, occurs when an unauthorized user gains access to a victim’s account using the account’s login credentials. The account details may be purchased on the dark web or obtained through phishing or other forms of social engineering.
With BNPL, the fraudster uses the stolen account information to buy items that they will receive in the place of the account holder. The fraudster typically redirects deliveries to a neutral location, sometimes called a drop address, that has no connection to either party, making the theft harder to trace. The victim may not realize what has happened until payments start coming due on their account weeks or even months later.
New account fraud occurs when a fraudster successfully opens a new account at a bank or payment service for the purpose of committing fraud. Everyone has a new banking or payments account at some point, even multiple new accounts, and most of these are legitimate. But some people open an account with the intention of wrongdoing.
Opening a BNPL account is designed to be quick and easy, which is part of the product's appeal. That same ease, however, means some accounts are opened specifically to commit fraud. Fraudsters use stolen or fabricated information to create new accounts, make purchases, and walk away before repayment obligations kick in.
In some cases, the person making the purchase is exactly who they say they are, but they have no intention of repaying from the start. This is sometimes called first party fraud or first installment default: a genuine consumer opens a legitimate account, completes a real purchase, and then defaults on payments, often after receiving the goods.
A related pattern is friendly fraud, where a consumer falsely claims they did not authorize a transaction in order to initiate a chargeback while keeping both the product and the refund. Both behaviors are harder to detect than external fraud because there is no stolen identity to flag and no compromised account to trace.
Graph analytics, or network analytics, is a powerful component of any tech stack used to detect and investigate buy now, pay later fraud. Rather than examining individual data points in isolation, graph technology analyzes both the data points themselves and the relationships between them. It works across customers, devices, transactions, and locations, and handles large volumes of data without slowing down the investigation.
This is particularly relevant for BNPL fraud, where the most damaging schemes typically involve groups of fraudsters working across multiple fake identities, accounts, and platforms. One suspicious application might not raise a flag on its own. But when several applications share the same address, phone number, or device, the pattern becomes hard to ignore.
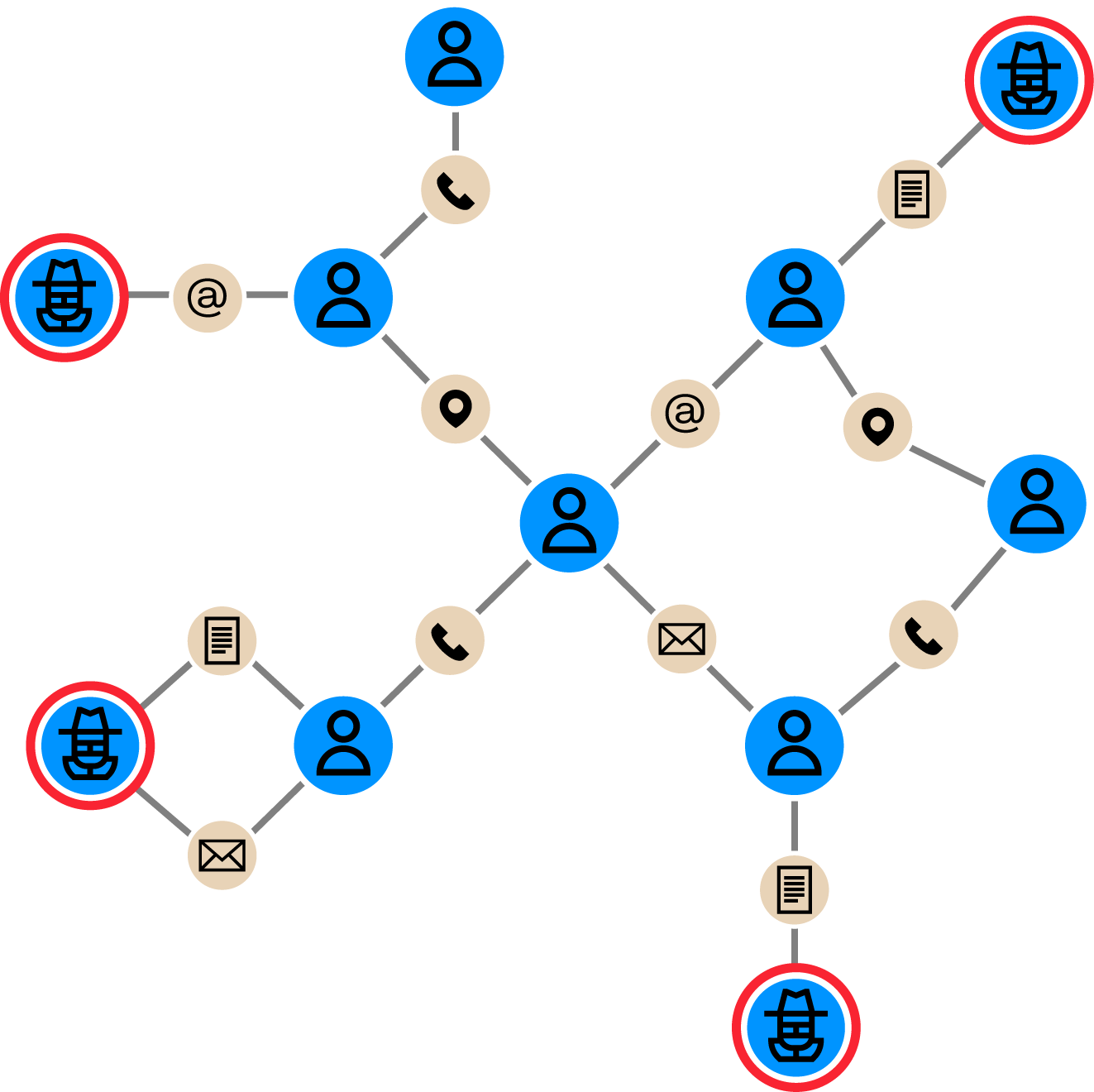
Say that as a BNPL provider, your company is facing networks of fraudsters acquiring loans through synthetic identities and then not paying them back. You have a risk scoring engine that can score and reject applications, but you’re not sure of the efficiency of the rules. Using a graph-native investigation tool like Linkurious Enterprise, you can look for communities of credit requests through personally identifiable information (PII) and digital footprints.
By visualizing rejected credit requests and their direct and indirect connections, you can quickly identify fraudsters that may have duped the risk scoring engine. And that information can then be fed back into the scoring engine to strengthen anti-fraud defenses.
Want to go deeper? Watch a demo about how to use graph analytics to expose BNPL fraud rings:
A spotlight on graph technology directly in your inbox.