Mule accounts and money laundering: How to eliminate blindspots in detection and investigation
Money laundering is an ongoing and significant challenge for financial institutions worldwide, with criminals constantly evolving their tactics to evade detection. One common money laundering scheme is the use of money mules and mule accounts. These seemingly innocent individuals or businesses play a crucial role in moving illicit funds, creating a buffer between criminals and their ill-gotten gains.
As financial institutions aim to combat this growing threat, they face the complex task of identifying and investigating mule accounts amidst a sea of legitimate accounts, customers, and transactions. This article explores the role of mule accounts in the money laundering process and the red flags that may indicate mule activity. We'll also take a look at how cutting-edge analytics technology is revolutionizing the way financial analysts are able to detect and investigate these elusive accounts, providing a powerful tool in the ongoing fight against financial crime.
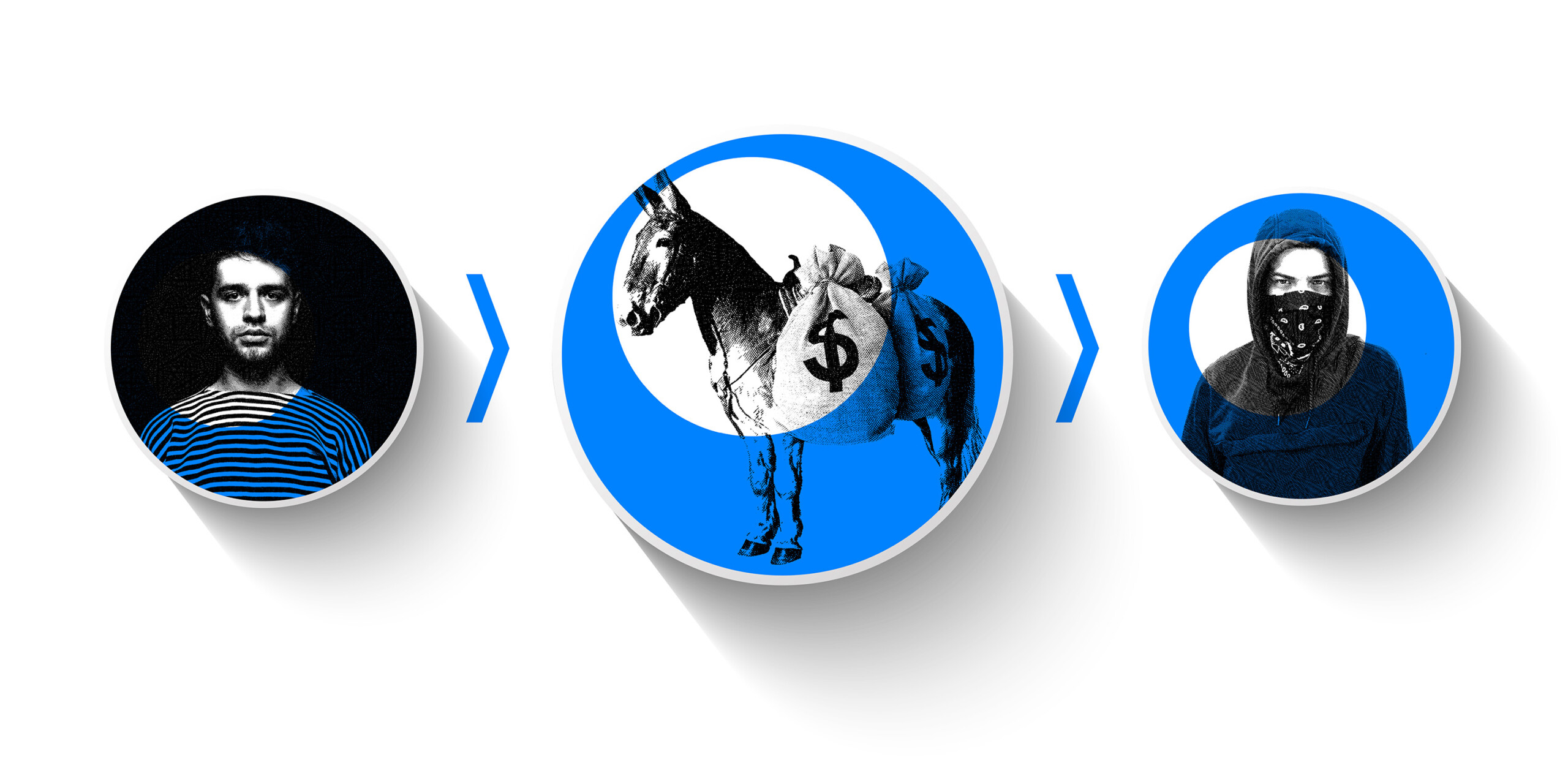
Money muling, also called mule fraud, is when a person or a business moves or transfers ill-gotten funds for someone else. The owner of the funds may be trying to distance themselves from those assets because they have illegal origins: fraud, or drug or human trafficking. The account used by a money mule is called a mule account.
The ideal money mule is someone who is apparently unconnected to the criminal group trying to hide the sources of their money. Relying on a mule creates distance between criminals and their money, making it more difficult for law enforcement to trace trails of dirty money.
Criminal groups tend to target financially or emotionally vulnerable people to operate mule accounts. Traditionally the typical profile of a money mule has included students (and especially international students who can more easily slip across borders), job seekers, or even individuals on dating sites. About 23% of money mules are under 21, and 65% are below 30.
Some mules receive a commission for their work. Some may be manipulated into believing they are helping out a friend or romantic partner. And some are unwitting mule fraud victims, unaware they are participating in criminal activity. Aware or not, money mules can suffer serious consequences if they are caught. They can be excluded from accessing bank accounts or loans for years, and may even be sentenced to jail time.
A mule account or money mule is generally part of the first phase of money laundering, called placement, in which illicit funds are integrated into the financial system. The account may be opened using the mule’s actual personal information, or using a synthetic identity.
Once the mule account is opened within a bank or other payment service, money is deposited in that account. The mule then receives instructions on how the funds should be moved and where they should go. Next, the mule transfers the funds to another account. They might also withdraw them as cash to be deposited elsewhere.
An essential step in tackling mule fraud is knowing when to investigate an account or a customer - either an individual or a business - for mule activity. Some common money mule red flags include:
- Changes in transactional behavior, including sudden international transfers, large purchases of crypto currency, or other large non-typical transfers
- Rapid movement of funds through the account with little to no balance retention
- Multiple cash deposits just under reporting thresholds, followed by rapid transfers
- Accounts with minimal activity suddenly receiving large incoming transfers
- Abnormalities identified via online behavior, such as hesitation inputting data, keystroke delays, etc.
- Round dollar amount purchases that are frequent and/or in large amounts, which can indicate gift card purchases for money muling
- Absence of typical account behavior.
As a part of their anti-money laundering activities, banks and financial institutions must continually screen for potential mule accounts and conduct investigations on any suspicious activity. Failure to establish sufficient safeguards against mule accounts can lead to fines from regulators.
But mule accounts can often resemble legitimate accounts. Criminals also frequently change their tactics, which can make it challenging to keep risk models up to date. Younger people have traditionally been the target recruits for money muling, for example. But according to Cifas statistics, the number of 40-60 year olds involved in activity bearing the hallmarks of money muling has increased by a third between 2017 and 2021.
Professional criminals are also good at evading traditional rules-based systems, keeping their activity - and the activity of those working for them - under thresholds that would raise a red flag. Furthermore, with little or no apparent links between a criminal organization and their money mules, understanding the extent of mule networks can be challenging.
Effectively investigating mule accounts is largely a question of data and context. Data and the relationships between entities show analysts who is transferring money where, who has relationships with whom, which entities share information, etc. All essential information in determining whether or not an account is engaging in mule activity. Investigating a mule account is largely about identifying the networks around that account and how they operate.
Graph analytics works in a way that’s perfectly suited to analyze both individual data points and the relationship between them to deliver context. Graph technology is based on a data structure that consists of a set of nodes and edges (or relationships). Each node represents an entity, such as a person, a bank account, an address or any other piece of data. Each edge represents how two nodes are linked to each other.
Analyzing and understanding relationships is much easier than with tools based on traditional data models.
Financial crime detection and investigation software that is built using graph technology, such as Linkurious Enterprise, offers robust solutions for managing mule account risk and investigating suspicious activity.
Rules-based alert systems are able to catch most of the suspicious behavior associated with mule accounts. For example, this kind of system will generate an alert if a certain amount of money is being transferred within a defined timeframe, or if there is a mismatch between a business’s declared activity and the amounts of money flowing through their account.
Graph analytics offers several specific advantages for the detection and investigation of suspicious activity, particularly when it is associated with complex money mule schemes. First, graph technology provides powerful capabilities to spot and connect multiple weak signals that can be indicative of mule accounts rings. It also enables analysts to gain deeper context and insight to quickly understand the full extent of a mule scam. This ensures they get to the bottom of the problem - which may go beyond the individual flagged account.
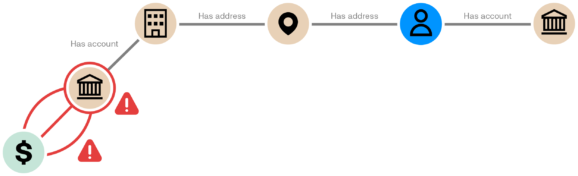
Using graph visualization, you can quickly see where money has been transferred and in what amounts, which will be a strong indicator of which other accounts may be implicated in money laundering activity. You can also quickly identify links through personal information. A business account that has been flagged as suspicious may turn out to be registered to the same address as an individual. That person will merit additional investigation.
Graph visualization shows these relationships in a couple of clicks, speeding up investigations and ensuring no money mules fly under the radar.
When layered onto existing systems, graph technology is a powerful tool to help analysts quickly understand all the connections between customers, transactions, accounts, and more. The result is faster, more effective money mule investigations and less compliance risk for financial institutions.
Graph analytics is a powerful tool to fight back against money laundering and other financial crime. Download our white paper to learn how graph-powered next-generation financial crime detection and investigation software can help detect more fraud and money laundering schemes and significantly speed up investigations.
A spotlight on graph technology directly in your inbox.