How do you protect yourself when the threat is coming from within? Internal fraud, also called insider fraud, poses a threat to organizations worldwide. On average, they lose 5% of their annual revenue to fraud each year, with nearly half of that attributed to internal, employee-driven fraud. In the US alone, some $50 billion is lost to internal fraud annually. And as companies face increasing economic uncertainty, the incentives and pressures that can lead good employees down the path of fraud have never been greater.
At the same time, detection and investigation tools too often fall short, focusing too much on individual signals and red flags scattered across data silos. They fail to show investigators the big picture with full context—meaning important signals and more complex fraud schemes fall through the cracks.
This article looks at what internal fraud is, along with some common insider fraud schemes. It also discusses some of the challenges of detecting and investigating this type of fraud—and how graph-native investigation technology is offering solutions aligned with modern insider threats.
Internal fraud happens when employees in a company use deceptive or illegal conduct to gain money or other benefits. This can include many different types of schemes:
- Insider trading
- Asset misappropriation
- HR & payroll fraud
- Data, IP & theft
- Embezzlement
- Financial statement fraud
- Expense reimbursement fraud
- Procurement fraud
- Etc.
Insider fraud is different from fraud perpetrated by outsiders because it hinges on employee access to a company's own systems and knowledge.
Sometimes insider fraud is carried out in collusion with external accomplices. That was the case in a scheme named in a lawsuit by Amazon. The filing revealed how an organized crime group used methods that included working with Amazon employees to process fake refunds in exchange for bribes, enriching the fraudsters.
All together, these schemes are both prevalent and costly:
- 57% of fraud is committed by company insiders or a combination of insiders and outsiders.
- The median internal fraud loss according to the ACFE is $145,000, but of course that can vary widely according to the type of fraud, type of organization, the number of accomplices, and more.
- Overall the financial services industry is the most impacted by internal fraud.
Insiders pose a particular threat to organizations because they possess the knowledge to manipulate internal systems to their own benefit. They might have access to funds, sensitive data, or restricted systems as part of their job. They also may know company policies around fraud, as well as the hallmarks of fraud their organization looks out for, to better fly under the radar.
Breaches or misuse may therefore go undetected for longer since they can more easily go undetected than a hack or break-in at the hands of an outsider would.
The tools and techniques used to detect insider fraud can fall short. Often, they flag individual incidents or behavior. But fraud is inherently relational, with the true scope of fraud only emerging through patterns or networks. Traditional tools may not sufficiently contextualize data, leaving some suspicious activity undetected.
“It’s rare that a single piece of information proves fraud,” said Guillaume Parisot of Ecosys Group, who discussed their innovative technical set-up for internal fraud detection in a recent webinar. “It’s several weak signals together that signal suspicious behavior.”
Finally, both data and defenses are all too often siloed within organizations. Cybersecurity, compliance, AML operations, corporate security, risk management, etc. may all operate separately with little communication or data sharing. This makes it easier for insiders manipulating internal systems to slip through the cracks and evade detection for longer.
With internal fraud being particularly difficult to spot and investigate, classic fraud detection approaches often leave suspicious behavior unseen. This is because data is naturally siloed by application: purchases, accounting, supplier repositories, banking, validation tools, etc. “Each tool tells part of the story,” says Guillaume Parisot, “but the links between objects are not visible in the same place (like who is linked to whom, and how.)”
Because of these limitations, detection and investigation tools built on graph technology offer a more effective solution to fraud analysts. Because graph technology puts the connections within data front and center, it gathers and makes the relationships between disparate data readable. You can navigate from a payment to an account, a supplier, an invoice, a representative, etc.—without manually reconstructing those links.
The result? Analysts can move faster from the initial signal to investigation, and the investigation becomes sharable and traceable.
Ecosys Group built an internal fraud investigation model for a client using graph investigation technology from Linkurious, as demonstrated during a recent webinar. The client needed a way to detect fraud and risky behavior that allowed them to fully explore relationships, and make their investigations auditable.
The result was a central investigation space where, starting from one signal, investigators can trace any relevant links to see the big picture around that entity of interest: accounts, suppliers, invoices, representatives, etc. This graph-based investigation solution also allowed the client to move from “one-shot” investigations to a surveillance model. Identified fraud patterns can now be monitored systematically.
Watch the replay to take a deep dive into the case study:
Fraud investigators examining potential cases of internal fraud need to prove complicity in a scheme. Graph can help emphasize the connections between bad actors and fraud incidents to show what’s really going on.
Let’s look at how graph visualization and analytics can be applied to a specific internal fraud use case where it can greatly increase detection and investigation efficiency.
For more use cases read our ebook on the subject. You’ll learn how to use graph visualization and analytics to track down internal fraud schemes like:
- Billing schemes
- Asset misappropriation
- False sales and shipping schemes
- Phishing using internal data
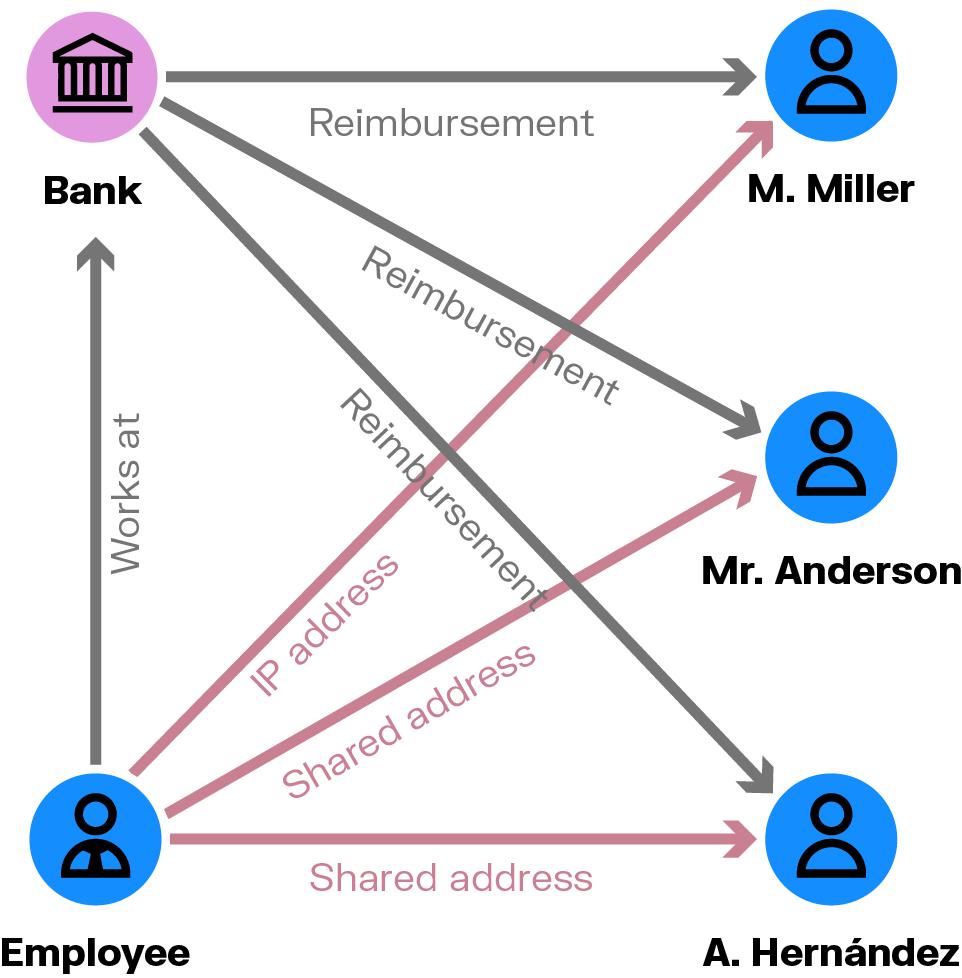
Chargeback fraud is a common problem for banks, and one that poses a big opportunity for collusive insider agents. Someone working at a financial institution may have insider information on how to “game” the system. They might know how to obtain a fraudulent reimbursement, for example, and share that information with friends and family so they can profit.
Graph can show you the social and personal connections that indicate who the individuals taking advantage of the system may be colluding with inside your organization. Does an employee share a home address with someone who has committed fraud? What about their social media connections? Individuals colluding on a chargeback scheme may also share an IP address or devices, such as the smartphone or computer used to access the banking app. A graph will enable you to quickly visualize these kinds of relationships.
There is an urgent need for a shift in how organizations detect and investigate internal fraud. Traditional methods are proving insufficient in the context of rapid digital transformation and the complex networks that characterize modern fraud schemes. But advanced technologies like graph analytics offer a more interconnected and dynamic approach to fraud detection.
For a deeper look at leveraging such technology against the threat of internal fraud, download our comprehensive e-book. It expands on the concepts discussed here, offering more detailed insights and real-world examples.
A spotlight on graph technology directly in your inbox.